As systems become more connected and AI accelerates both innovation and risk, the traditional model—servers, plugins, patches, and internal oversight—no longer holds. Most organizations aren’t managing infrastructure anymore; they’re operating inside platforms. Security in this environment isn’t defined by a single system. It’s a stack of layers working together.
The First Layer: Domain and DNS
Every website begins with a domain—yourcompany.com.
That domain is typically managed through providers like GoDaddy or Network Solutions. These platforms do not host your website. They simply act as a directory, pointing users to wherever your site actually lives.
This connection is made through DNS records—essentially instructions that route traffic.
It's important to understand what this means:
- The domain is not your website
- It does not contain your content
- It does not define your security
It's a pointer.
Security at this layer is about control—who has access to the domain account, and whether those routing instructions are correctly configured. Once traffic leaves this layer, it moves into the platform itself.

Your domain is the front door to your entire digital presence. It should be protected with the same level of control and oversight as your financial accounts—owned, secured, and managed by a responsible officer within your organization.
The Second Layer: CMS and Editor Access
The next point of exposure is human.
Who can log in?
Who can publish content?
Who has permission to make changes?
Modern platforms like Webflow manage this through structured access:
- Role-based permissions
- Secure login environments
- Optional multi-step verification for added protection
This is where most real-world risk occurs—not in infrastructure, but in access.
A well-managed system limits who can do what, and ensures that publishing power is intentional, not accidental.

The Third Layer: Structure and Content Systems
Security is also shaped by how a website is built.
Traditional websites often rely on open systems—plugins, third-party tools, and custom code layered together over time. Each addition introduces variability, and with it, potential risk.
Modern platforms take a different approach.
- Content is structured.
- Templates are controlled.
- Design systems define how information is created and displayed.
This reduces unpredictability.
When a system is consistent, it's easier to manage, easier to audit, and far less likely to introduce unintended vulnerabilities. The absence of a sprawling plugin ecosystem isn't a limitation—it's a deliberate constraint that reduces exposure.
The Fourth Layer: The Hosting Platform
This is where the most significant shift has occurred.
In a traditional model, hosting meant servers—maintained, updated, and secured by internal teams or third-party vendors. Responsibility was fragmented.
Webflow operates differently.
It is a managed platform, meaning:
- There is no direct server access
- There are no control panels to maintain
- There are no patches to apply manually
Security is handled centrally.
The platform is continuously updated, monitored, and audited against established standards for how systems manage and protect data (often referred to as SOC 2 compliance). These audits are not one-time events—they are ongoing validations of how the platform operates.
For marketing teams, this removes an entire category of responsibility.
You are not securing a server.
You are operating within a secured system.

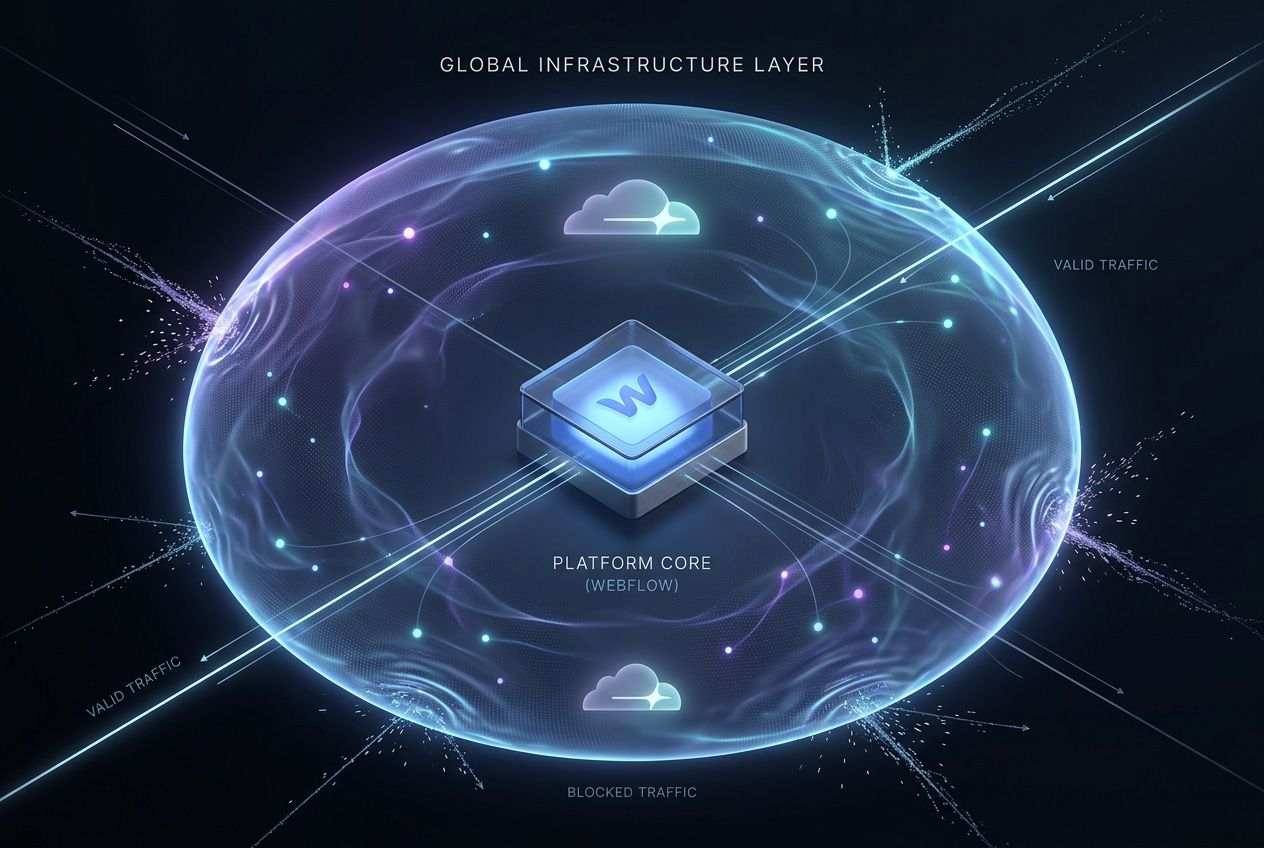
The Fifth Layer: The Network
Before a visitor ever reaches your website, their request passes through a global network.
This is where infrastructure companies like Cloudflare operate.
Their role is to:
- Manage incoming traffic
- Filter out malicious activity
- Distribute load across a global system
If someone attempts to overwhelm a website with traffic—a common form of attack often called a distributed denial-of-service (DDoS) attack—this network absorbs and neutralizes it before it ever reaches the platform.
In simple terms:
The website is protected before it is even touched.
This layer operates continuously and invisibly, adapting in real time to patterns that would be impossible to manage manually.
The AI Reality
AI is changing the nature of risk.
Attacks are no longer isolated or slow-moving. They are automated, scalable, and persistent. The speed at which systems can be probed, tested, and exploited has increased dramatically.
This creates a gap.
Manual security practices—updates, patches, monitoring—cannot keep pace with automated threats.
The only viable response is to shift security upstream:
- Into platforms
- Into infrastructure
- Into systems designed to adapt continuously

What This Means for Marketing Teams
For most organizations, this isn't about technical control. It's about operational clarity.
The internal IT footprint shrinks. The points of failure across fragmented tools shrink with it. Deployment gets faster without adding new risk, and compliance becomes easier to demonstrate rather than defend.
Security becomes embedded in how the system works—not something layered on after the fact.
A Different Way to Think About Risk
The question is no longer “Is this website secure?”—it’s “Who is responsible for keeping it secure?”
In traditional systems, that responsibility is spread across hosting providers, plugins, third-party tools, and internal teams. Each layer introduces its own dependencies and potential gaps. Modern platforms consolidate most of that responsibility—handling infrastructure, updates, and core security within a single, managed environment.
There are still a few external control points, and DNS is one of them. The domain provider (such as GoDaddy or Bluehost) acts as the entry point that routes traffic to the platform. If that layer is misconfigured or compromised, it can redirect users regardless of how secure the underlying system is. In an AI-driven world, the real risk is not just exposure—it’s fragmentation. Strong security comes from reducing the number of systems in play, and tightly controlling the few that remain.
